 How Hardware Gets Hacked (Part 2): On-boarding
How Hardware Gets Hacked (Part 2): On-boarding
Explore a hardware security workflow using firmware builds, simulation tools, serial commands, and automated tests for microcontroller systems.
 Accelerating the evolution of smart robotics and autonomous machines
Accelerating the evolution of smart robotics and autonomous machines
From collaborative robots on factory floors to autonomous mobile robots in dynamic environments, learn how ADI’s innovative technologies deliver real-time perception, localization, motion control, and secure connectivity—enabling smarter, safer, and more adaptable machines.
 Webinar - Why Cybersecurity Belongs in Safety Conversations
Webinar - Why Cybersecurity Belongs in Safety Conversations
Safety components that once operated in isolation now communicate across networks bringing tremendous value, but it also creating risk.
 Nsing Technologies
Nsing Technologies
NSING Technologies Pte. Ltd was founded in 2018 at the heart of Singapore, a group of talented and dedicated engineers teamed together to realize the same goal – bring more high-performance semiconductor products and solutions to global semiconductor industry.
 Meeting Cyber Resilience Act Requirements with Hardware Root of Trust
Meeting Cyber Resilience Act Requirements with Hardware Root of Trust
The European Cyber Resilience Act (CRA) aims to improve the security of products with digital components with mandatory cybersecurity requirements.
 Choosing the Right Memory Architecture for Firmware Security
Choosing the Right Memory Architecture for Firmware Security
Firmware security has always been an afterthought. Therefore, the choice of memory architecture is a key decision in establishing a verifiable chain of trust.
 Secure Embedded Solutions
Publish Date: 2025-12-31
Secure Embedded Solutions
Publish Date: 2025-12-31
STMicroelectronics is creating a portfolio of secure embedded systems that simplify cyber resilience act (CRA) compliance. Learn how to design for cyber security now!
 How Hardware Gets Hacked (Part 1)
How Hardware Gets Hacked (Part 1)
Learn how embedded systems face physical attacks, key fob risks, competition challenges, and common weaknesses in hardware security.
 Accelerate Advanced IoT Deployment with Multiprotocol Wireless MCU Modules
Publish Date: 2025-12-12
Accelerate Advanced IoT Deployment with Multiprotocol Wireless MCU Modules
Publish Date: 2025-12-12
Learn how multiradio wireless MCU modules accelerate the design, certification, and deployment of advanced multiprotocol IoT devices.
 How To Monitor Login Attempts on a Raspberry Pi
How To Monitor Login Attempts on a Raspberry Pi
Create your own Raspberry Pi intrusion detector by logging all successful and failed SSH, local, and VNC login attempts to detect suspicious access activity.
Many semiconductor production environments rely on standalone software security systems resulting in a malware risk via USB flash drives or maintenance PCs.
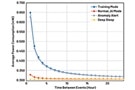
 Use Optimized IR Emitters to Minimize Performance Tradeoffs
Use Optimized IR Emitters to Minimize Performance Tradeoffs
Advanced IR emitters offer high performance and consistent operation, with a broad range of devices to best meet application priorities.

OPTIGA Authenticate NBT helps users bring effortless, secure and ultra-fast NFC connectivity to IoT designs.
 Apply an Edge AI Drop-In Solution to Enhance Wireless Condition-Based Monitoring
Publish Date: 2025-09-30
Apply an Edge AI Drop-In Solution to Enhance Wireless Condition-Based Monitoring
Publish Date: 2025-09-30
A drop-in solution with edge AI enables immediate deployment of wireless condition-based monitoring with real-time notification of vibration anomalies.
 Use Advanced Analog Front-Ends and Security to Bring Benefits of AI to Medical Point of Care
Publish Date: 2025-09-24
Use Advanced Analog Front-Ends and Security to Bring Benefits of AI to Medical Point of Care
Publish Date: 2025-09-24
The accelerating trend towards point-of-care medical tests and assessments requires sophisticated, application-focused analog front-end and data security ICs.
 iWave Telematics Solutions Aligned with International & EU Cybersecurity Standards
iWave Telematics Solutions Aligned with International & EU Cybersecurity Standards
With the rapid expansion of connected automotive and telematics systems, cybersecurity has become non-negotiable - telematics devices must be secure by design.
 Uncovering Vibration Monitoring VOYAGER4 Essentials for Practicing Engineers
Publish Date: 2025-09-18
Uncovering Vibration Monitoring VOYAGER4 Essentials for Practicing Engineers
Publish Date: 2025-09-18
Wireless vibration monitoring evaluation kit supports condition-based monitoring of motors in robotics, pumps, fans, wind turbines, and other systems.
 Cybersecurity regulations: A paradigm shift
Cybersecurity regulations: A paradigm shift
This webinar will delve into the changing landscape of security regulations.
 Use Flexible AFE, Motion Control, and Authentication ICs to Design Point of Care Diagnostics Systems
Publish Date: 2025-04-22
Use Flexible AFE, Motion Control, and Authentication ICs to Design Point of Care Diagnostics Systems
Publish Date: 2025-04-22
Designers need flexible and application-focused analog front-end, motion-control, and authentication ICs to realize point-of-care medical test benefits.
 Webinar – Cybersecurity Regulations: A Paradigm Shift
Webinar – Cybersecurity Regulations: A Paradigm Shift
Keep up to date on cutting edge cybersecurity including the most recent regulations and legislation establishing security standards for digital products.







